Dxr.axd Exploit Review
GET /dxr.axd?path=/../../Windows/win.ini HTTP/1.1
Alex remembered a passing mention from a senior colleague: “ dxr.axd is an old mapping handler in some ASP.NET apps. If it’s misconfigured, it can be tricked into serving any file.” dxr.axd exploit
That night shift taught Alex that exploits don’t always arrive with flashing red lights. Sometimes they whisper through a forgotten .axd file—and listening closely can save the whole system. GET /dxr
His heart rate ticked up. This wasn’t a random scan—the ..\..\ pattern was a path traversal attempt, trying to climb out of the web root and read system files. His heart rate ticked up
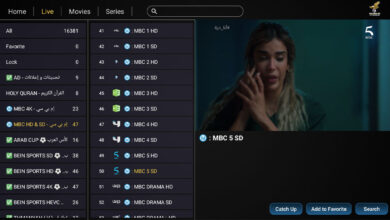
In the gray hours of a late shift, Alex, a junior security analyst at a mid-sized retail company, stared at a flood of alerts. Most were noise—false positives from marketing tools, a misconfigured printer, someone trying to stream video on a work PC. But one line in the web server log caught his eye: